spinnaker概述和选型 概述 主要功能 Spinnaker是一个开源的多云持续交付平台,提供快速、可靠、稳定的软件变更服务。主要包含两类功能:集群管理和部署管理
集群管理 集群管理主要用于管理云资源,Spinnaker所说的”云“可以理解成AWS,即主要是laaS的资源,比如OpenStak,Google云,微软云等,后来还支持了容器与Kubernetes,但是管理方式还是按照管理基础设施的模式来设计的。
部署管理 管理部署流程是Spinnaker的核心功能,使用minio作为持久化层,同时对接jenkins流水线创建的镜像,部署到Kubernetes集群中去,让服务真正运行起来。
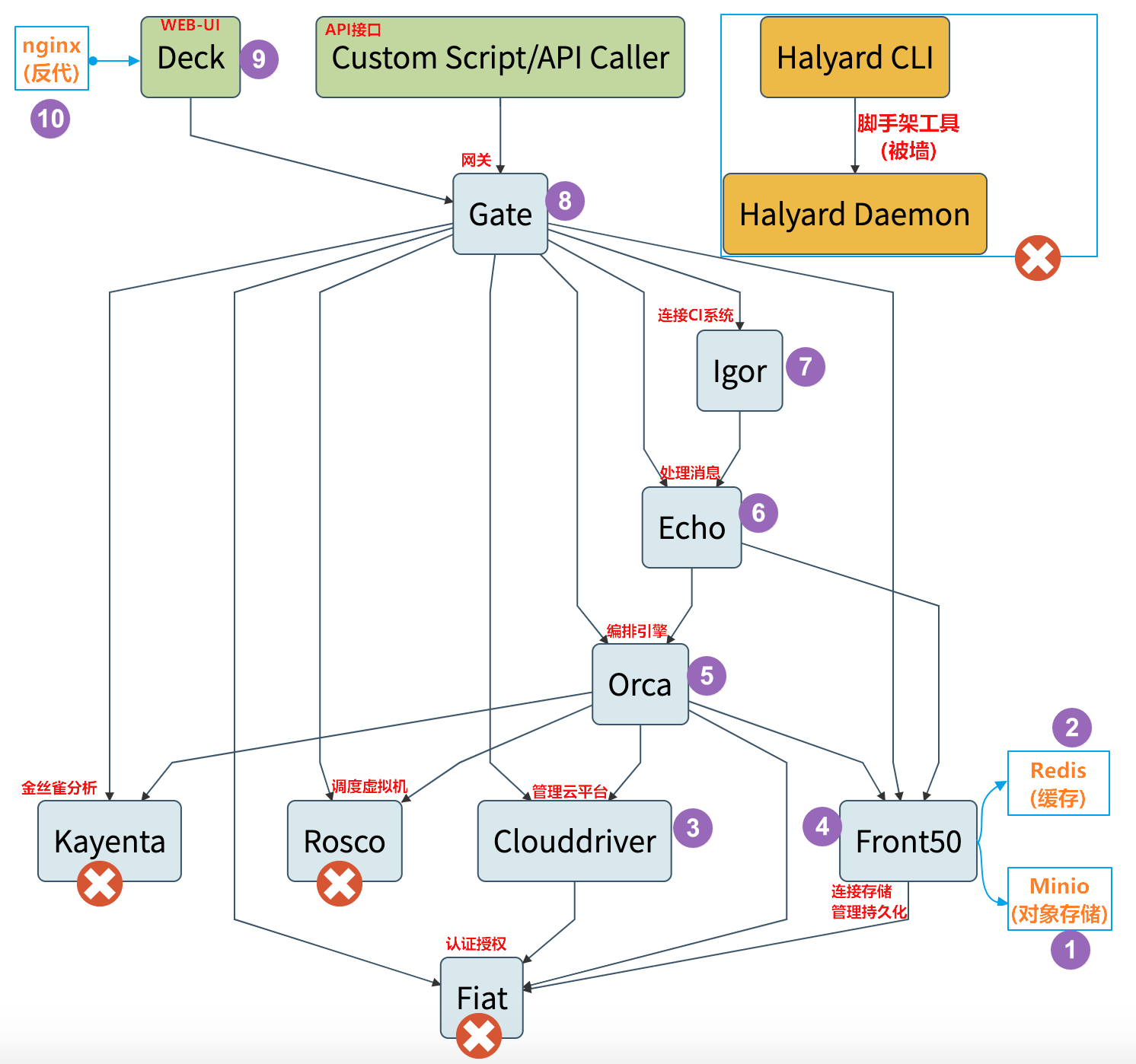
逻辑架构图 Spinnaker自己就是Spinnake一个微服务,由若干组件组成,整套逻辑架构图如下:
Deck 是基于浏览器的UI。Gate 是API网关。Clouddriver 负责管理云平台,并为所有部署的资源编制索引/缓存。Front50 用于管理数据持久化,用于保存应用程序,管道,项目和通知的元数据。Igor 用于通过Jenkins和Travis CI等系统中的持续集成作业来触发管道,并且它允许在管道中使用Jenkins / Travis阶段。Orca 是编排引擎。它处理所有临时操作和流水线。Rosco 是管理调度虚拟机。Kayenta 为Spinnaker提供自动化的金丝雀分析。Fiat 是Spinnaker的认证服务。Echo 是信息通信服务。部署选型 Spinnaker官网 Armory发行版
因此我们部署的方式是手动交付Spinnaker的Armory发行版
建议: VMware 虚拟机给node01和node02节点4-5g,俩核
部署spinnaker第一部分 spinnaker之minio部署 准备minio镜像 在k8s-dns上:
1 2 3 docker pull minio/minio:latest docker tag minio/minio:latest harbor.od.com/armory/minio:latest docker push harbor.od.com/armory/minio:latest
准备资源配置清单 1 2 3 mkdir /var/k8s-yaml/armory/minio -p cd /var/k8s-yaml/armory/minio/ mkdir /data/nfs-volume/minio
vim /var/k8s-yaml/armory/minio/dp.yaml
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 kind: Deployment apiVersion: apps/v1 kind: Deployment metadata: labels: name: minio name: minio namespace: armory spec: progressDeadlineSeconds: 600 replicas: 1 revisionHistoryLimit: 7 selector: matchLabels: name: minio template: metadata: labels: app: minio name: minio spec: containers: - name: minio image: harbor.od.com/armory/minio:latest imagePullPolicy: IfNotPresent ports: - containerPort: 9000 protocol: TCP args: - server - "--console-address" - ":9001" - /data env: - name: MINIO_ACCESS_KEY value: admin - name: MINIO_SECRET_KEY value: admin123 readinessProbe: failureThreshold: 3 httpGet: path: /minio/health/ready port: 9000 scheme: HTTP initialDelaySeconds: 10 periodSeconds: 10 successThreshold: 1 timeoutSeconds: 5 volumeMounts: - mountPath: /data name: data imagePullSecrets: - name: harbor volumes: - nfs: server: k8s-dns path: /data/nfs-volume/minio name: data
注意: 最新版需要修改args:参数。
vim /var/k8s-yaml/armory/minio/svc.yaml
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 apiVersion: v1 kind: Service metadata: name: minio namespace: armory spec: ports: - name: api port: 9000 targetPort: 9000 protocol: TCP - name: consle port: 80 targetPort: 9001 protocol: TCP selector: app: minio
注意: 最新版需要监听9001。
vim /var/k8s-yaml/armory/minio/ingress.yaml
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 kind: Ingress apiVersion: extensions/v1beta1 metadata: name: minio namespace: armory spec: rules: - host: minio.od.com http: paths: - path: / backend: serviceName: minio servicePort: 80 - host: minio-api.od.com http: paths: - path: / backend: serviceName: minio servicePort: 9000
dns解析记录 1 2 3 4 [root@k8s-dns ~]# vi /var/named/chroot/etc/od.com.zone ... minio A 10.1.1.50 minio-api A 10.1.1.50 # 提供给front50使用的api
应用配置清单 在任意一台k8s运算节点执行:
1 2 3 4 5 6 7 8 9 10 11 kubectl create namespace armory kubectl create secret docker-registry harbor \ --docker-server=harbor.od.com \ --docker-username=admin \ --docker-password=Harbor12345 \ -n armory # 应用清单 kubectl apply -f http://k8s-yaml.od.com/armory/minio/dp.yaml kubectl apply -f http://k8s-yaml.od.com/armory/minio/svc.yaml kubectl apply -f http://k8s-yaml.od.com/armory/minio/ingress.yaml
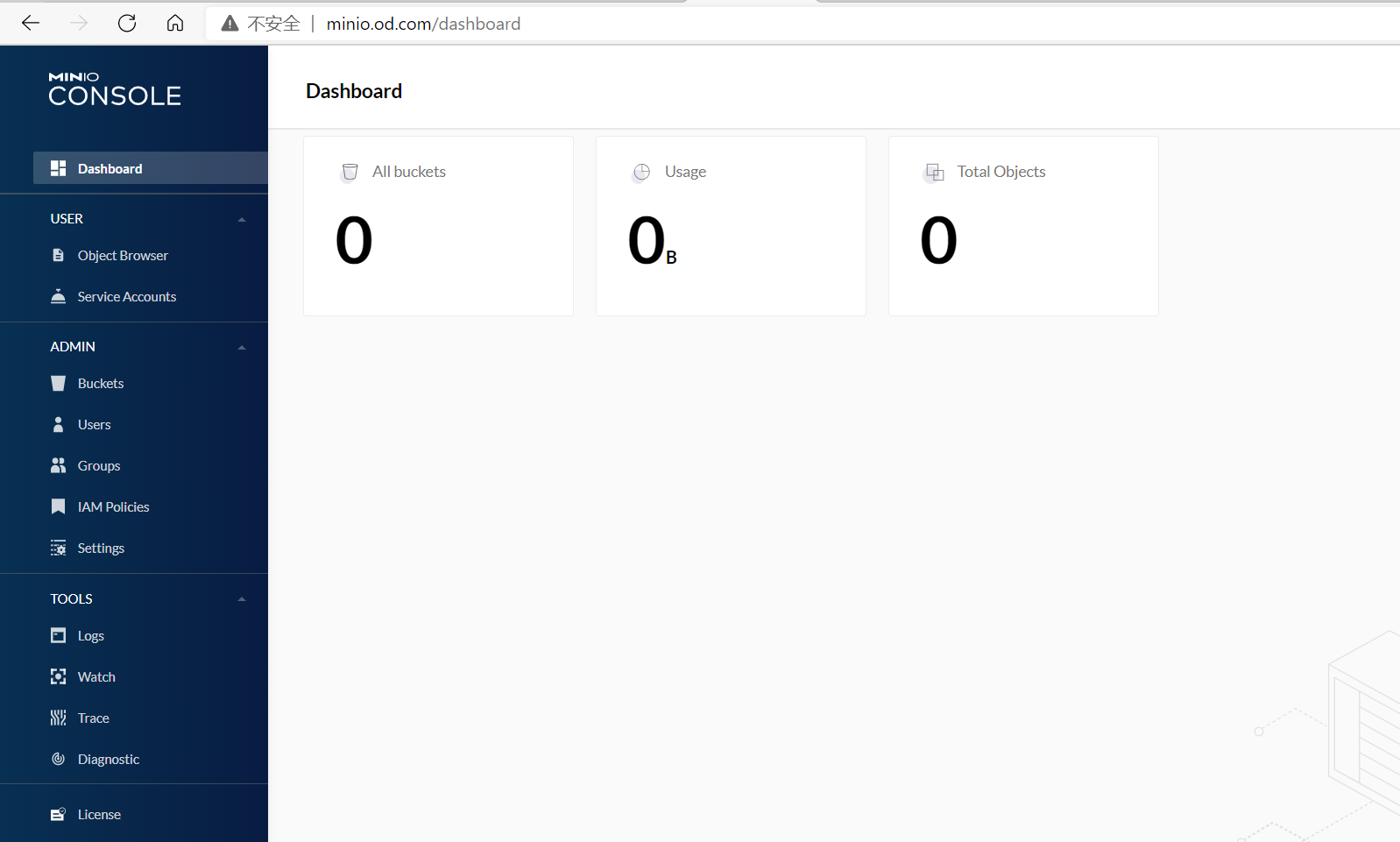
访问验证 访问http://minio.od.com
用户名密码为:admin/admin123新版界面有些变化。
redis部署 准备镜像好目录 1 2 3 docker pull redis:5.0 docker tag redis:5.0 harbor.od.com/armory/redis:v5.0 docker push harbor.od.com/armory/redis:v5.0
准备资源配置清单 1 2 mkdir -p /var/k8s-yaml/armory/redis cd /var/k8s-yaml/armory/redis
vim /var/k8s-yaml/armory/redis/dp.yaml
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 kind: Deployment apiVersion: apps/v1 metadata: labels: name: redis name: redis namespace: armory spec: replicas: 1 revisionHistoryLimit: 7 selector: matchLabels: name: redis template: metadata: labels: app: redis name: redis spec: containers: - name: redis image: harbor.od.com/armory/redis:v5.0 imagePullPolicy: IfNotPresent ports: - containerPort: 6379 protocol: TCP imagePullSecrets: - name: harbor
vim /var/k8s-yaml/armory/redis/svc.yaml
1 2 3 4 5 6 7 8 9 10 11 12 apiVersion: v1 kind: Service metadata: name: redis namespace: armory spec: ports: - port: 6379 protocol: TCP targetPort: 6379 selector: app: redis
应用资源配置清单 在任意一台k8s运算节点执行:
1 2 kubectl apply -f http://k8s-yaml.od.com/armory/redis/dp.yaml kubectl apply -f http://k8s-yaml.od.com/armory/redis/svc.yaml
检查验证 1 2 3 4 5 6 kubectl get svc -n armory -o wide telnet 192.168.105.106 6379 Trying 192.168.105.106... Connected to 192.168.105.106. Escape character is '^]'. info
部署spinnaker之CloudDriver CloudDriver是整套spinnaker部署中最难的部分,相当于spinnaker大脑。
部署准备工作 准备镜像和目录 1 2 3 docker pull armory/spinnaker-clouddriver-slim:release-1.11.x-bee52673a docker tag armory/spinnaker-clouddriver-slim:release-1.11.x-bee52673a harbor.od.com/armory/clouddriver:v1.11.x docker push harbor.od.com/armory/clouddriver:v1.11.x
准备目录
1 2 mkdir /var/k8s-yaml/armory/clouddriver cd /var/k8s-yaml/armory/clouddriver
准备minio的secret 准备配置文件
1 2 3 4 5 cat >credentials <<'EOF' [default] aws_access_key_id=admin aws_secret_access_key=admin123 EOF
在任意一台k8s运算节点执行:
1 2 3 4 5 6 7 8 9 10 11 wget http://k8s-yaml.od.com/armory/clouddriver/credentials kubectl create secret generic credentials \ --from-file=./credentials \ -n armory # kubectl create secret generic credentials \ --aws_access_key_id=admin \ --aws_secret_access_key=admin123 \ -n armory
签发证书与私钥 在k8s-dns.boysec.cn上
1 2 3 4 5 6 7 8 9 10 cd /opt/certs cp client-csr.json admin-csr.json sed -i 's#k8s-node#cluster-admin#g' admin-csr.json cfssl gencert \ -ca=ca.pem \ -ca-key=ca-key.pem \ -config=ca-config.json \ -profile=client \ admin-csr.json |cfssljson -bare admin ls admin*
分发证书 在任意一台k8s运算节点执行:
1 2 3 4 cd /opt/certs scp k8s-dns:/opt/certs/ca.pem . scp k8s-dns:/opt/certs/admin.pem . scp k8s-dns:/opt/certs/admin-key.pem .
创建用户 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 # 4步法创建用户 kubectl config set-cluster myk8s \ --certificate-authority=/opt/crets/ca.pem \ --embed-certs=true --server=https://10.1.1.50:7443 \ --kubeconfig=config kubectl config set-credentials cluster-admin \ --client-certificate=/opt/crets/admin.pem \ --client-key=/opt/crets/admin-key.pem \ --embed-certs=true --kubeconfig=config kubectl config set-context myk8s-context \ --cluster=myk8s \ --user=cluster-admin \ --kubeconfig=config kubectl config use-context myk8s-context \ --kubeconfig=config # 集群角色绑定 kubectl create clusterrolebinding myk8s-admin \ --clusterrole=cluster-admin \ --user=cluster-admin
验证及其他主机远程管理集群 1 2 3 4 5 6 7 8 [root@k8s-node01 ~]# kubectl config view apiVersion: v1 clusters: null contexts: null current-context: "" kind: Config preferences: {} users: null
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 [root@k8s-node01 ~]# cp config .kube/ [root@k8s-node01 ~]# kubectl config view apiVersion: v1 clusters: - cluster: certificate-authority-data: DATA+OMITTED server: https://10.1.1.50:7443 name: myk8s contexts: - context: cluster: myk8s user: cluster-admin name: myk8s-context current-context: myk8s-context kind: Config preferences: {} users: - name: cluster-admin user: client-certificate-data: REDACTED client-key-data: REDACTED
注意: 这样kubectl管理工具就是通过vip来访问apiserver
在k8s-dns.boysec.cn上:
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 [root@k8s-dns ~]# mkdir .kube [root@k8s-dns ~]# scp k8s-node01:/root/.kube/config .kube/ [root@k8s-dns ~]# scp k8s-node01:/opt/kubernetes/server/bin/kubectl /usr/bin/ [root@k8s-dns ~]# kubectl config view apiVersion: v1 clusters: - cluster: certificate-authority-data: DATA+OMITTED server: https://10.1.1.50:7443 name: myk8s contexts: - context: cluster: myk8s user: cluster-admin name: myk8s-context current-context: myk8s-context kind: Config preferences: {} users: - name: cluster-admin user: client-certificate-data: REDACTED client-key-data: REDACTED
使用config创建cm资源 1 2 cp config default-kubeconfig kubectl create cm default-kubeconfig --from-file=default-kubeconfig -n armory
创建资源配置清单 ConfigMap1 ConfigMap2 ConfigMap3 Deployment Service vim /var/k8s-yaml/armory/clouddriver/default-config.yaml
注意:此配置文件超长,是用armory部署工具部署好后,基本不需要改动
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 108 109 110 111 112 113 114 115 116 117 118 119 120 121 122 123 124 125 126 127 128 129 130 131 132 133 134 135 136 137 138 139 140 141 142 143 144 145 146 147 148 149 150 151 152 153 154 155 156 157 158 159 160 161 162 163 164 165 166 167 168 169 170 171 172 173 174 175 176 177 178 179 180 181 182 183 184 185 186 187 188 189 190 191 192 193 194 195 196 197 198 199 200 201 202 203 204 205 206 207 208 209 210 211 212 213 214 215 216 217 218 219 220 221 222 223 224 225 226 227 228 229 230 231 232 233 234 235 236 237 238 239 240 241 242 243 244 245 246 247 248 249 250 251 252 253 254 255 256 257 258 259 260 261 262 263 264 265 266 267 268 269 270 271 272 273 274 275 276 277 278 279 280 281 282 283 284 285 286 287 288 289 290 291 292 293 294 295 296 297 298 299 300 301 302 303 304 305 306 307 308 309 310 311 312 313 314 315 316 317 318 319 320 321 322 323 324 325 326 327 328 329 330 331 332 333 334 335 336 337 338 339 340 341 342 343 344 345 346 347 348 349 350 351 352 353 354 355 356 357 358 359 360 361 362 363 364 365 366 367 368 369 370 371 372 373 374 375 376 377 378 379 380 381 382 383 384 385 386 387 388 389 390 391 392 393 394 395 396 397 398 399 400 401 402 403 404 405 406 407 408 409 410 411 412 413 414 415 416 417 418 419 420 421 422 423 424 425 426 427 428 429 430 431 432 433 434 435 436 437 438 439 440 441 442 443 444 445 446 447 448 449 450 451 452 453 454 455 456 457 458 459 460 461 462 463 464 465 466 467 468 469 470 471 472 473 474 475 476 477 478 479 480 481 482 483 484 485 486 487 488 489 490 491 492 493 494 495 496 497 498 499 500 501 502 503 504 505 506 507 508 509 510 511 512 513 514 515 516 517 518 519 520 521 522 523 524 525 526 527 528 529 530 531 532 533 534 535 536 537 538 539 540 541 542 543 544 545 546 547 548 549 550 551 552 553 554 555 556 557 558 559 560 561 562 563 564 565 566 567 568 569 570 571 572 573 574 575 576 577 578 579 580 581 582 583 584 585 586 587 588 589 590 591 592 593 594 595 596 597 598 599 600 601 602 603 604 605 606 607 608 609 610 611 612 613 614 615 616 617 618 619 620 621 622 623 624 625 626 627 628 629 630 631 632 633 634 635 636 637 638 639 640 641 642 643 644 645 646 647 648 649 650 651 652 653 654 655 656 657 658 659 660 661 662 663 664 665 666 667 668 669 670 671 672 673 674 675 676 677 678 679 680 681 682 683 684 685 686 687 688 689 690 691 692 693 694 695 696 697 698 699 700 701 702 703 704 705 706 707 708 709 710 711 712 713 714 715 716 717 718 719 720 721 722 723 724 725 726 727 728 729 730 731 732 733 734 735 736 737 738 739 740 741 742 743 744 745 746 747 748 749 750 751 752 753 754 755 756 757 758 759 760 761 762 763 764 765 766 767 768 769 770 771 772 773 774 775 776 777 778 779 780 781 782 783 784 785 786 787 788 789 790 791 792 793 794 795 796 797 798 799 800 801 802 803 804 805 806 807 808 809 810 811 812 813 814 815 816 817 818 819 820 821 822 823 824 825 826 827 828 829 830 831 832 833 834 835 836 837 838 839 840 841 842 843 844 845 846 847 848 849 850 851 852 853 854 855 856 857 858 859 860 861 862 863 864 865 866 867 868 869 870 871 872 873 874 875 876 877 878 879 880 881 882 883 884 885 886 887 888 889 890 891 892 893 894 895 896 897 898 899 900 901 902 903 904 905 906 907 908 909 910 911 912 913 914 915 916 917 918 919 920 921 922 923 924 925 926 927 928 929 930 931 932 933 934 935 936 937 938 939 940 941 942 943 944 945 946 947 948 949 950 951 952 953 954 955 956 957 958 959 960 961 962 963 964 965 966 967 968 969 970 971 972 973 974 975 976 977 978 979 980 981 982 983 984 985 986 987 988 989 990 991 992 993 994 995 996 997 998 999 1000 1001 1002 1003 1004 1005 1006 1007 1008 1009 1010 1011 1012 1013 1014 1015 1016 1017 1018 1019 1020 1021 1022 1023 1024 1025 1026 1027 1028 1029 1030 1031 1032 1033 1034 1035 1036 1037 1038 1039 1040 1041 1042 1043 1044 1045 1046 1047 1048 1049 1050 1051 1052 1053 1054 1055 1056 1057 1058 1059 1060 1061 1062 1063 1064 1065 1066 1067 1068 1069 1070 1071 1072 1073 1074 1075 1076 1077 1078 1079 1080 1081 1082 1083 1084 1085 1086 1087 1088 1089 1090 1091 1092 1093 1094 1095 1096 1097 1098 1099 1100 1101 1102 1103 1104 1105 1106 1107 1108 1109 1110 1111 1112 1113 1114 1115 1116 1117 1118 1119 1120 1121 1122 1123 1124 1125 1126 1127 1128 1129 1130 1131 1132 1133 1134 1135 1136 1137 1138 1139 1140 1141 1142 1143 1144 1145 1146 1147 1148 1149 1150 1151 1152 1153 1154 1155 1156 1157 1158 1159 1160 1161 1162 1163 1164 1165 1166 1167 1168 1169 1170 1171 1172 1173 1174 1175 1176 1177 1178 1179 1180 1181 1182 1183 1184 1185 1186 1187 1188 1189 1190 1191 1192 1193 1194 1195 1196 1197 1198 1199 1200 1201 1202 1203 1204 1205 1206 1207 1208 1209 1210 1211 1212 1213 1214 1215 1216 1217 1218 1219 1220 1221 1222 1223 1224 1225 1226 1227 1228 1229 1230 1231 1232 1233 1234 1235 1236 1237 1238 1239 1240 1241 1242 1243 1244 1245 1246 1247 1248 1249 1250 1251 1252 1253 1254 1255 1256 1257 1258 1259 1260 1261 1262 1263 1264 1265 1266 1267 1268 1269 1270 1271 1272 1273 1274 1275 1276 1277 1278 1279 1280 1281 1282 1283 1284 1285 1286 1287 1288 1289 1290 1291 1292 1293 1294 1295 1296 1297 1298 1299 1300 1301 1302 1303 1304 1305 1306 1307 1308 1309 1310 1311 1312 1313 1314 1315 1316 1317 1318 1319 1320 1321 1322 1323 1324 1325 1326 1327 1328 1329 1330 1331 1332 1333 1334 1335 1336 1337 1338 1339 1340 1341 1342 1343 1344 1345 1346 1347 1348 1349 1350 1351 1352 1353 1354 1355 1356 1357 1358 1359 1360 1361 1362 1363 1364 1365 1366 1367 1368 1369 1370 1371 1372 kind: ConfigMap apiVersion: v1 metadata: name: default-config namespace: armory data: barometer.yml: | server: port: 9092 spinnaker: redis: host: ${services.redis.host} port: ${services.redis.port} clouddriver-armory.yml: | aws: defaultAssumeRole: role/${SPINNAKER_AWS_DEFAULT_ASSUME_ROLE:SpinnakerManagedProfile} accounts: - name: default-aws-account accountId: ${SPINNAKER_AWS_DEFAULT_ACCOUNT_ID:none} client: maxErrorRetry: 20 serviceLimits: cloudProviderOverrides: aws: rateLimit: 15.0 implementationLimits: AmazonAutoScaling: defaults: rateLimit: 3.0 AmazonElasticLoadBalancing: defaults: rateLimit: 5.0 security.basic.enabled: false management.security.enabled: false clouddriver-dev.yml: | serviceLimits: defaults: rateLimit: 2 clouddriver.yml: | server: port: ${services.clouddriver.port:7002} address: ${services.clouddriver.host:localhost} redis: connection: ${REDIS_HOST:redis://localhost:6379} udf: enabled: ${services.clouddriver.aws.udf.enabled:true} udfRoot: /opt/spinnaker/config/udf defaultLegacyUdf: false default: account: env: ${providers.aws.primaryCredentials.name} aws: enabled: ${providers.aws.enabled:false} defaults: iamRole: ${providers.aws.defaultIAMRole:BaseIAMRole} defaultRegions: - name: ${providers.aws.defaultRegion:us-east-1} defaultFront50Template: ${services.front50.baseUrl} defaultKeyPairTemplate: ${providers.aws.defaultKeyPairTemplate} azure: enabled: ${providers.azure.enabled:false} accounts: - name: ${providers.azure.primaryCredentials.name} clientId: ${providers.azure.primaryCredentials.clientId} appKey: ${providers.azure.primaryCredentials.appKey} tenantId: ${providers.azure.primaryCredentials.tenantId} subscriptionId: ${providers.azure.primaryCredentials.subscriptionId} google: enabled: ${providers.google.enabled:false} accounts: - name: ${providers.google.primaryCredentials.name} project: ${providers.google.primaryCredentials.project} jsonPath: ${providers.google.primaryCredentials.jsonPath} consul: enabled: ${providers.google.primaryCredentials.consul.enabled:false} cf: enabled: ${providers.cf.enabled:false} accounts: - name: ${providers.cf.primaryCredentials.name} api: ${providers.cf.primaryCredentials.api} console: ${providers.cf.primaryCredentials.console} org: ${providers.cf.defaultOrg} space: ${providers.cf.defaultSpace} username: ${providers.cf.account.name:} password: ${providers.cf.account.password:} kubernetes: enabled: ${providers.kubernetes.enabled:false} accounts: - name: ${providers.kubernetes.primaryCredentials.name} dockerRegistries: - accountName: ${providers.kubernetes.primaryCredentials.dockerRegistryAccount} openstack: enabled: ${providers.openstack.enabled:false} accounts: - name: ${providers.openstack.primaryCredentials.name} authUrl: ${providers.openstack.primaryCredentials.authUrl} username: ${providers.openstack.primaryCredentials.username} password: ${providers.openstack.primaryCredentials.password} projectName: ${providers.openstack.primaryCredentials.projectName} domainName: ${providers.openstack.primaryCredentials.domainName:Default} regions: ${providers.openstack.primaryCredentials.regions} insecure: ${providers.openstack.primaryCredentials.insecure:false} userDataFile: ${providers.openstack.primaryCredentials.userDataFile:} lbaas: pollTimeout: 60 pollInterval: 5 dockerRegistry: enabled: ${providers.dockerRegistry.enabled:false} accounts: - name: ${providers.dockerRegistry.primaryCredentials.name} address: ${providers.dockerRegistry.primaryCredentials.address} username: ${providers.dockerRegistry.primaryCredentials.username:} passwordFile: ${providers.dockerRegistry.primaryCredentials.passwordFile} credentials: primaryAccountTypes: ${providers.aws.primaryCredentials.name}, ${providers.google.primaryCredentials.name}, ${providers.cf.primaryCredentials.name}, ${providers.azure.primaryCredentials.name} challengeDestructiveActionsEnvironments: ${providers.aws.primaryCredentials.name}, ${providers.google.primaryCredentials.name}, ${providers.cf.primaryCredentials.name}, ${providers.azure.primaryCredentials.name} spectator: applicationName: ${spring.application.name} webEndpoint: enabled: ${services.spectator.webEndpoint.enabled:false} prototypeFilter: path: ${services.spectator.webEndpoint.prototypeFilter.path:} stackdriver: enabled: ${services.stackdriver.enabled} projectName: ${services.stackdriver.projectName} credentialsPath: ${services.stackdriver.credentialsPath} stackdriver: hints: - name: controller.invocations labels: - account - region dinghy.yml: "" echo-armory.yml: | diagnostics: enabled: true id: ${ARMORY_ID:unknown} armorywebhooks: enabled: false forwarding: baseUrl: http://armory-dinghy:8081 endpoint: v1/webhooks echo-noncron.yml: | scheduler: enabled: false echo.yml: | server: port: ${services.echo.port:8089} address: ${services.echo.host:localhost} cassandra: enabled: ${services.echo.cassandra.enabled:false} embedded: ${services.cassandra.embedded:false} host: ${services.cassandra.host:localhost} spinnaker: baseUrl: ${services.deck.baseUrl} cassandra: enabled: ${services.echo.cassandra.enabled:false} inMemory: enabled: ${services.echo.inMemory.enabled:true} front50: baseUrl: ${services.front50.baseUrl:http://localhost:8080 } orca: baseUrl: ${services.orca.baseUrl:http://localhost:8083 } endpoints.health.sensitive: false slack: enabled: ${services.echo.notifications.slack.enabled:false} token: ${services.echo.notifications.slack.token} spring: mail: host: ${mail.host} mail: enabled: ${services.echo.notifications.mail.enabled:false} host: ${services.echo.notifications.mail.host} from: ${services.echo.notifications.mail.fromAddress} hipchat: enabled: ${services.echo.notifications.hipchat.enabled:false} baseUrl: ${services.echo.notifications.hipchat.url} token: ${services.echo.notifications.hipchat.token} twilio: enabled: ${services.echo.notifications.sms.enabled:false} baseUrl: ${services.echo.notifications.sms.url:https://api.twilio.com/ } account: ${services.echo.notifications.sms.account} token: ${services.echo.notifications.sms.token} from: ${services.echo.notifications.sms.from} scheduler: enabled: ${services.echo.cron.enabled:true} threadPoolSize: 20 triggeringEnabled: true pipelineConfigsPoller: enabled: true pollingIntervalMs: 30000 cron: timezone: ${services.echo.cron.timezone} spectator: applicationName: ${spring.application.name} webEndpoint: enabled: ${services.spectator.webEndpoint.enabled:false} prototypeFilter: path: ${services.spectator.webEndpoint.prototypeFilter.path:} stackdriver: enabled: ${services.stackdriver.enabled} projectName: ${services.stackdriver.projectName} credentialsPath: ${services.stackdriver.credentialsPath} webhooks: artifacts: enabled: true fetch.sh: |+ CONFIG_LOCATION=${SPINNAKER_HOME:-"/opt/spinnaker"}/config CONTAINER=$1 rm -f /opt/spinnaker/config/*.yml mkdir -p ${CONFIG_LOCATION} for filename in /opt/spinnaker/config/default/*.yml; do cp $filename ${CONFIG_LOCATION} done if [ -d /opt/spinnaker/config/custom ]; then for filename in /opt/spinnaker/config/custom/*; do cp $filename ${CONFIG_LOCATION} done fi add_ca_certs() { ca_cert_path="$1" jks_path="$2" alias="$3" if [[ "$(whoami)" != "root" ]]; then echo "INFO: I do not have proper permisions to add CA roots" return fi if [[ ! -f $ {ca_cert_path } ]]; then echo "INFO: No CA cert found at ${ca_cert_path}" return fi keytool -importcert \ -file $ {ca_cert_path } \ -keystore $ {jks_path } \ -alias $ {alias } \ -storepass changeit \ -noprompt } if [ `which keytool` ]; then echo "INFO: Keytool found adding certs where appropriate" add_ca_certs "${CONFIG_LOCATION}/ca.crt" "/etc/ssl/certs/java/cacerts" "custom-ca" else echo "INFO: Keytool not found, not adding any certs/private keys" fi saml_pem_path="/opt/spinnaker/config/custom/saml.pem" saml_pkcs12_path="/tmp/saml.pkcs12" saml_jks_path="${CONFIG_LOCATION}/saml.jks" x509_ca_cert_path="/opt/spinnaker/config/custom/x509ca.crt" x509_client_cert_path="/opt/spinnaker/config/custom/x509client.crt" x509_jks_path="${CONFIG_LOCATION}/x509.jks" x509_nginx_cert_path="/opt/nginx/certs/ssl.crt" if [ "${CONTAINER}" == "gate" ]; then if [ -f $ {saml_pem_path } ]; then echo "Loading ${saml_pem_path} into ${saml_jks_path}" openssl pkcs12 -export -out ${saml_pkcs12_path} -in ${saml_pem_path} -password pass:changeit -name saml keytool -genkey -v -keystore ${saml_jks_path} -alias saml \ -keyalg RSA -keysize 2048 -validity 10000 \ -storepass changeit -keypass changeit -dname "CN=armory" keytool -importkeystore \ -srckeystore ${saml_pkcs12_path} \ -srcstoretype PKCS12 \ -srcstorepass changeit \ -destkeystore ${saml_jks_path} \ -deststoretype JKS \ -storepass changeit \ -alias saml \ -destalias saml \ -noprompt else echo "No SAML IDP pemfile found at ${saml_pem_path}" fi if [ -f $ {x509_ca_cert_path } ]; then echo "Loading ${x509_ca_cert_path} into ${x509_jks_path}" add_ca_certs ${x509_ca_cert_path} ${x509_jks_path} "ca" else echo "No x509 CA cert found at ${x509_ca_cert_path}" fi if [ -f $ {x509_client_cert_path } ]; then echo "Loading ${x509_client_cert_path} into ${x509_jks_path}" add_ca_certs ${x509_client_cert_path} ${x509_jks_path} "client" else echo "No x509 Client cert found at ${x509_client_cert_path}" fi if [ -f $ {x509_nginx_cert_path } ]; then echo "Creating a self-signed CA (EXPIRES IN 360 DAYS) with java keystore: ${x509_jks_path}" echo -e "\n\n\n\n\n\ny\n" | keytool -genkey -keyalg RSA -alias server -keystore keystore.jks -storepass changeit -validity 360 -keysize 2048 keytool -importkeystore \ -srckeystore keystore.jks \ -srcstorepass changeit \ -destkeystore "${x509_jks_path}" \ -storepass changeit \ -srcalias server \ -destalias server \ -noprompt else echo "No x509 nginx cert found at ${x509_nginx_cert_path}" fi fi if [ "${CONTAINER}" == "nginx" ]; then nginx_conf_path="/opt/spinnaker/config/default/nginx.conf" if [ -f $ {nginx_conf_path } ]; then cp ${nginx_conf_path} /etc/nginx/nginx.conf fi fi fiat.yml: |- server: port: ${services.fiat.port:7003} address: ${services.fiat.host:localhost} redis: connection: ${services.redis.connection:redis://localhost:6379} spectator: applicationName: ${spring.application.name} webEndpoint: enabled: ${services.spectator.webEndpoint.enabled:false} prototypeFilter: path: ${services.spectator.webEndpoint.prototypeFilter.path:} stackdriver: enabled: ${services.stackdriver.enabled} projectName: ${services.stackdriver.projectName} credentialsPath: ${services.stackdriver.credentialsPath} hystrix: command: default.execution.isolation.thread.timeoutInMilliseconds: 20000 logging: level: com.netflix.spinnaker.fiat: DEBUG front50-armory.yml: | spinnaker: redis: enabled: true host: redis front50.yml: | server: port: ${services.front50.port:8080} address: ${services.front50.host:localhost} hystrix: command: default.execution.isolation.thread.timeoutInMilliseconds: 15000 cassandra: enabled: ${services.front50.cassandra.enabled:false} embedded: ${services.cassandra.embedded:false} host: ${services.cassandra.host:localhost} aws: simpleDBEnabled: ${providers.aws.simpleDBEnabled:false} defaultSimpleDBDomain: ${providers.aws.defaultSimpleDBDomain} spinnaker: cassandra: enabled: ${services.front50.cassandra.enabled:false} host: ${services.cassandra.host:localhost} port: ${services.cassandra.port:9042} cluster: ${services.cassandra.cluster:CASS_SPINNAKER} keyspace: front50 name: global redis: enabled: ${services.front50.redis.enabled:false} gcs: enabled: ${services.front50.gcs.enabled:false} bucket: ${services.front50.storage_bucket:} bucketLocation: ${services.front50.bucket_location:} rootFolder: ${services.front50.rootFolder:front50} project: ${providers.google.primaryCredentials.project} jsonPath: ${providers.google.primaryCredentials.jsonPath} s3: enabled: ${services.front50.s3.enabled:false} bucket: ${services.front50.storage_bucket:} rootFolder: ${services.front50.rootFolder:front50} spectator: applicationName: ${spring.application.name} webEndpoint: enabled: ${services.spectator.webEndpoint.enabled:false} prototypeFilter: path: ${services.spectator.webEndpoint.prototypeFilter.path:} stackdriver: enabled: ${services.stackdriver.enabled} projectName: ${services.stackdriver.projectName} credentialsPath: ${services.stackdriver.credentialsPath} stackdriver: hints: - name: controller.invocations labels: - application - cause - name: aws.request.httpRequestTime labels: - status - exception - AWSErrorCode - name: aws.request.requestSigningTime labels: - exception gate-armory.yml: |+ lighthouse: baseUrl: http://${DEFAULT_DNS_NAME:lighthouse}:5000 gate.yml: | server: port: ${services.gate.port:8084} address: ${services.gate.host:localhost} redis: connection: ${REDIS_HOST:redis://localhost:6379} configuration: secure: true spectator: applicationName: ${spring.application.name} webEndpoint: enabled: ${services.spectator.webEndpoint.enabled:false} prototypeFilter: path: ${services.spectator.webEndpoint.prototypeFilter.path:} stackdriver: enabled: ${services.stackdriver.enabled} projectName: ${services.stackdriver.projectName} credentialsPath: ${services.stackdriver.credentialsPath} stackdriver: hints: - name: EurekaOkClient_Request labels: - cause - reason - status igor-nonpolling.yml: | jenkins: polling: enabled: false igor.yml: | server: port: ${services.igor.port:8088} address: ${services.igor.host:localhost} jenkins: enabled: ${services.jenkins.enabled:false} masters: - name: ${services.jenkins.defaultMaster.name} address: ${services.jenkins.defaultMaster.baseUrl} username: ${services.jenkins.defaultMaster.username} password: ${services.jenkins.defaultMaster.password} csrf: ${services.jenkins.defaultMaster.csrf:false} travis: enabled: ${services.travis.enabled:false} masters: - name: ${services.travis.defaultMaster.name} baseUrl: ${services.travis.defaultMaster.baseUrl} address: ${services.travis.defaultMaster.address} githubToken: ${services.travis.defaultMaster.githubToken} dockerRegistry: enabled: ${providers.dockerRegistry.enabled:false} redis: connection: ${REDIS_HOST:redis://localhost:6379} spectator: applicationName: ${spring.application.name} webEndpoint: enabled: ${services.spectator.webEndpoint.enabled:false} prototypeFilter: path: ${services.spectator.webEndpoint.prototypeFilter.path:} stackdriver: enabled: ${services.stackdriver.enabled} projectName: ${services.stackdriver.projectName} credentialsPath: ${services.stackdriver.credentialsPath} stackdriver: hints: - name: controller.invocations labels: - master kayenta-armory.yml: | kayenta: aws: enabled: ${ARMORYSPINNAKER_S3_ENABLED:false} accounts: - name: aws-s3-storage bucket: ${ARMORYSPINNAKER_CONF_STORE_BUCKET} rootFolder: kayenta supportedTypes: - OBJECT_STORE - CONFIGURATION_STORE s3: enabled: ${ARMORYSPINNAKER_S3_ENABLED:false} google: enabled: ${ARMORYSPINNAKER_GCS_ENABLED:false} accounts: - name: cloud-armory bucket: ${ARMORYSPINNAKER_CONF_STORE_BUCKET} rootFolder: kayenta-prod supportedTypes: - METRICS_STORE - OBJECT_STORE - CONFIGURATION_STORE gcs: enabled: ${ARMORYSPINNAKER_GCS_ENABLED:false} kayenta.yml: |2 server: port: 8090 kayenta: atlas: enabled: false google: enabled: false aws: enabled: false datadog: enabled: false prometheus: enabled: false gcs: enabled: false s3: enabled: false stackdriver: enabled: false memory: enabled: false configbin: enabled: false keiko: queue: redis: queueName: kayenta.keiko.queue deadLetterQueueName: kayenta.keiko.queue.deadLetters redis: connection: ${REDIS_HOST:redis://localhost:6379} spectator: applicationName: ${spring.application.name} webEndpoint: enabled: true swagger: enabled: true title: Kayenta API description: contact: patterns: - /admin.* - /canary.* - /canaryConfig.* - /canaryJudgeResult.* - /credentials.* - /fetch.* - /health - /judges.* - /metadata.* - /metricSetList.* - /metricSetPairList.* - /pipeline.* security.basic.enabled: false management.security.enabled: false nginx.conf: | user nginx; worker_processes 1; error_log /var/log/nginx/error.log warn; pid /var/run/nginx.pid; events { worker_connections 1024 ; } http { include /etc/nginx/mime.types; default_type application/octet-stream; log_format main '$remote_addr - $remote_user [$time_local] "$request" ' '$status $body_bytes_sent "$http_referer" ' '"$http_user_agent" "$http_x_forwarded_for"' ; access_log /var/log/nginx/access.log main; sendfile on; keepalive_timeout 65 ; include /etc/nginx/conf.d/*.conf; } stream { upstream gate_api { server armory-gate:8085; } server { listen 8085 ; proxy_pass gate_api; } } nginx.http.conf: | gzip on; gzip_types text/plain text/css application/json application/x-javascript text/xml application/xml application/xml+rss text/javascript application/vnd.ms-fontobject application/x-font-ttf font/opentype image/svg+xml image/x-icon; server { listen 80 ; listen [:: ]:80; location / { proxy_pass http://armory-deck/; } location /api/ { proxy_pass http://armory-gate:8084/; } location /slack/ { proxy_pass http://armory-platform:10000/; } rewrite ^/login(.*)$ /api/login$1 last; rewrite ^/auth(.*)$ /api/auth$1 last; } nginx.https.conf: | gzip on; gzip_types text/plain text/css application/json application/x-javascript text/xml application/xml application/xml+rss text/javascript application/vnd.ms-fontobject application/x-font-ttf font/opentype image/svg+xml image/x-icon; server { listen 80 ; listen [:: ]:80; return 301 https://$host$request_uri; } server { listen 443 ssl; listen [:: ]:443 ssl; ssl on; ssl_certificate /opt/nginx/certs/ssl.crt; ssl_certificate_key /opt/nginx/certs/ssl.key; location / { proxy_pass http://armory-deck/; } location /api/ { proxy_pass http://armory-gate:8084/; proxy_set_header Host $host; proxy_set_header X-Real-IP $proxy_protocol_addr; proxy_set_header X-Forwarded-For $proxy_protocol_addr; proxy_set_header X-Forwarded-Proto $scheme; } location /slack/ { proxy_pass http://armory-platform:10000/; } rewrite ^/login(.*)$ /api/login$1 last; rewrite ^/auth(.*)$ /api/auth$1 last; } orca-armory.yml: | mine: baseUrl: http://${services.barometer.host}:${services.barometer.port} pipelineTemplate: enabled: ${features.pipelineTemplates.enabled:false} jinja: enabled: true kayenta: enabled: ${services.kayenta.enabled:false} baseUrl: ${services.kayenta.baseUrl} jira: enabled: ${features.jira.enabled:false} basicAuth: "Basic ${features.jira.basicAuthToken}" url: ${features.jira.createIssueUrl} webhook: preconfigured: - label: Enforce Pipeline Policy description: Checks pipeline configuration against policy requirements type: enforcePipelinePolicy enabled: ${features.certifiedPipelines.enabled:false} url: "http://lighthouse:5000/v1/pipelines/${execution.application}/${execution.pipelineConfigId}?check_policy=yes" headers: Accept: - application/json method: GET waitForCompletion: true statusUrlResolution: getMethod statusJsonPath: $.status successStatuses: pass canceledStatuses: terminalStatuses: TERMINAL - label: "Jira: Create Issue" description: Enter a Jira ticket when this pipeline runs type: createJiraIssue enabled: ${jira.enabled} url: ${jira.url} customHeaders: "Content-Type": application/json Authorization: ${jira.basicAuth} method: POST parameters: - name: summary label: Issue Summary description: A short summary of your issue. - name: description label: Issue Description description: A longer description of your issue. - name: projectKey label: Project key description: The key of your JIRA project. - name: type label: Issue Type description: The type of your issue, e.g. "Task" , "Story" , etc. payload: | { "fields" : { "description": "${parameterValues['description']}", "issuetype": { "name": "${parameterValues['type']}" }, "project": { "key": "${parameterValues['projectKey']}" }, "summary": "${parameterValues['summary']}" } } waitForCompletion: false - label: "Jira: Update Issue" description: Update a previously created Jira Issue type: updateJiraIssue enabled: ${jira.enabled} url: "${execution.stages.?[type == 'createJiraIssue'][0]['context']['buildInfo']['self']}" customHeaders: "Content-Type": application/json Authorization: ${jira.basicAuth} method: PUT parameters: - name: summary label: Issue Summary description: A short summary of your issue. - name: description label: Issue Description description: A longer description of your issue. payload: | { "fields" : { "description": "${parameterValues['description']}", "summary": "${parameterValues['summary']}" } } waitForCompletion: false - label: "Jira: Transition Issue" description: Change state of existing Jira Issue type: transitionJiraIssue enabled: ${jira.enabled} url: "${execution.stages.?[type == 'createJiraIssue'][0]['context']['buildInfo']['self']}/transitions" customHeaders: "Content-Type": application/json Authorization: ${jira.basicAuth} method: POST parameters: - name: newStateID label: New State ID description: The ID of the state you want to transition the issue to. payload: | { "transition" : { "id" : "${parameterValues['newStateID']}" } } waitForCompletion: false - label: "Jira: Add Comment" description: Add a comment to an existing Jira Issue type: commentJiraIssue enabled: ${jira.enabled} url: "${execution.stages.?[type == 'createJiraIssue'][0]['context']['buildInfo']['self']}/comment" customHeaders: "Content-Type": application/json Authorization: ${jira.basicAuth} method: POST parameters: - name: body label: Comment body description: The text body of the component. payload: | { "body" : "${parameterValues['body']}" } waitForCompletion: false orca.yml: | server: port: ${services.orca.port:8083} address: ${services.orca.host:localhost} oort: baseUrl: ${services.oort.baseUrl:localhost:7002} front50: baseUrl: ${services.front50.baseUrl:localhost:8080} mort: baseUrl: ${services.mort.baseUrl:localhost:7002} kato: baseUrl: ${services.kato.baseUrl:localhost:7002} bakery: baseUrl: ${services.bakery.baseUrl:localhost:8087} extractBuildDetails: ${services.bakery.extractBuildDetails:true} allowMissingPackageInstallation: ${services.bakery.allowMissingPackageInstallation:true} echo: enabled: ${services.echo.enabled:false} baseUrl: ${services.echo.baseUrl:8089} igor: baseUrl: ${services.igor.baseUrl:8088} flex: baseUrl: http://not-a-host default: bake: account: ${providers.aws.primaryCredentials.name} securityGroups: vpc: securityGroups: redis: connection: ${REDIS_HOST:redis://localhost:6379} tasks: executionWindow: timezone: ${services.orca.timezone} spectator: applicationName: ${spring.application.name} webEndpoint: enabled: ${services.spectator.webEndpoint.enabled:false} prototypeFilter: path: ${services.spectator.webEndpoint.prototypeFilter.path:} stackdriver: enabled: ${services.stackdriver.enabled} projectName: ${services.stackdriver.projectName} credentialsPath: ${services.stackdriver.credentialsPath} stackdriver: hints: - name: controller.invocations labels: - application rosco-armory.yml: | redis: timeout: 50000 rosco: jobs: local: timeoutMinutes: 60 rosco.yml: | server: port: ${services.rosco.port:8087} address: ${services.rosco.host:localhost} redis: connection: ${REDIS_HOST:redis://localhost:6379} aws: enabled: ${providers.aws.enabled:false} docker: enabled: ${services.docker.enabled:false} bakeryDefaults: targetRepository: ${services.docker.targetRepository} google: enabled: ${providers.google.enabled:false} accounts: - name: ${providers.google.primaryCredentials.name} project: ${providers.google.primaryCredentials.project} jsonPath: ${providers.google.primaryCredentials.jsonPath} gce: bakeryDefaults: zone: ${providers.google.defaultZone} rosco: configDir: ${services.rosco.configDir} jobs: local: timeoutMinutes: 30 spectator: applicationName: ${spring.application.name} webEndpoint: enabled: ${services.spectator.webEndpoint.enabled:false} prototypeFilter: path: ${services.spectator.webEndpoint.prototypeFilter.path:} stackdriver: enabled: ${services.stackdriver.enabled} projectName: ${services.stackdriver.projectName} credentialsPath: ${services.stackdriver.credentialsPath} stackdriver: hints: - name: bakes labels: - success spinnaker-armory.yml: | armory: architecture: 'k8s' features: artifacts: enabled: true pipelineTemplates: enabled: ${PIPELINE_TEMPLATES_ENABLED:false} infrastructureStages: enabled: ${INFRA_ENABLED:false} certifiedPipelines: enabled: ${CERTIFIED_PIPELINES_ENABLED:false} configuratorEnabled: enabled: true configuratorWizard: enabled: true configuratorCerts: enabled: true loadtestStage: enabled: ${LOADTEST_ENABLED:false} jira: enabled: ${JIRA_ENABLED:false} basicAuthToken: ${JIRA_BASIC_AUTH} url: ${JIRA_URL} login: ${JIRA_LOGIN} password: ${JIRA_PASSWORD} slaEnabled: enabled: ${SLA_ENABLED:false} chaosMonkey: enabled: ${CHAOS_ENABLED:false} armoryPlatform: enabled: ${PLATFORM_ENABLED:false} uiEnabled: ${PLATFORM_UI_ENABLED:false} services: default: host: ${DEFAULT_DNS_NAME:localhost} clouddriver: host: ${DEFAULT_DNS_NAME:armory-clouddriver} entityTags: enabled: false configurator: baseUrl: http://${CONFIGURATOR_HOST:armory-configurator}:8069 echo: host: ${DEFAULT_DNS_NAME:armory-echo} deck: gateUrl: ${API_HOST:service.default.host} baseUrl: ${DECK_HOST:armory-deck} dinghy: enabled: ${DINGHY_ENABLED:false} host: ${DEFAULT_DNS_NAME:armory-dinghy} baseUrl: ${services.default.protocol}://${services.dinghy.host}:${services.dinghy.port} port: 8081 front50: host: ${DEFAULT_DNS_NAME:armory-front50} cassandra: enabled: false redis: enabled: true gcs: enabled: ${ARMORYSPINNAKER_GCS_ENABLED:false} s3: enabled: ${ARMORYSPINNAKER_S3_ENABLED:false} storage_bucket: ${ARMORYSPINNAKER_CONF_STORE_BUCKET} rootFolder: ${ARMORYSPINNAKER_CONF_STORE_PREFIX:front50} gate: host: ${DEFAULT_DNS_NAME:armory-gate} igor: host: ${DEFAULT_DNS_NAME:armory-igor} kayenta: enabled: true host: ${DEFAULT_DNS_NAME:armory-kayenta} canaryConfigStore: true port: 8090 baseUrl: ${services.default.protocol}://${services.kayenta.host}:${services.kayenta.port} metricsStore: ${METRICS_STORE:stackdriver} metricsAccountName: ${METRICS_ACCOUNT_NAME} storageAccountName: ${STORAGE_ACCOUNT_NAME} atlasWebComponentsUrl: ${ATLAS_COMPONENTS_URL:} lighthouse: host: ${DEFAULT_DNS_NAME:armory-lighthouse} port: 5000 baseUrl: ${services.default.protocol}://${services.lighthouse.host}:${services.lighthouse.port} orca: host: ${DEFAULT_DNS_NAME:armory-orca} platform: enabled: ${PLATFORM_ENABLED:false} host: ${DEFAULT_DNS_NAME:armory-platform} baseUrl: ${services.default.protocol}://${services.platform.host}:${services.platform.port} port: 5001 rosco: host: ${DEFAULT_DNS_NAME:armory-rosco} enabled: true configDir: /opt/spinnaker/config/packer bakery: allowMissingPackageInstallation: true barometer: enabled: ${BAROMETER_ENABLED:false} host: ${DEFAULT_DNS_NAME:armory-barometer} baseUrl: ${services.default.protocol}://${services.barometer.host}:${services.barometer.port} port: 9092 newRelicEnabled: ${NEW_RELIC_ENABLED:false} redis: host: redis port: 6379 connection: ${REDIS_HOST:redis://localhost:6379} fiat: enabled: ${FIAT_ENABLED:false} host: ${DEFAULT_DNS_NAME:armory-fiat} port: 7003 baseUrl: ${services.default.protocol}://${services.fiat.host}:${services.fiat.port} providers: aws: enabled: ${SPINNAKER_AWS_ENABLED:true} defaultRegion: ${SPINNAKER_AWS_DEFAULT_REGION:us-west-2} defaultIAMRole: ${SPINNAKER_AWS_DEFAULT_IAM_ROLE:SpinnakerInstanceProfile} defaultAssumeRole: ${SPINNAKER_AWS_DEFAULT_ASSUME_ROLE:SpinnakerManagedProfile} primaryCredentials: name: ${SPINNAKER_AWS_DEFAULT_ACCOUNT:default-aws-account} kubernetes: proxy: localhost:8001 apiPrefix: api/v1/proxy/namespaces/kube-system/services/kubernetes-dashboard/# spinnaker.yml: |2 global: spinnaker: timezone: 'Asia/Shanghai' architecture: ${PLATFORM_ARCHITECTURE} services: default: host: localhost protocol: http clouddriver: host: ${services.default.host} port: 7002 baseUrl: ${services.default.protocol}://${services.clouddriver.host}:${services.clouddriver.port} aws: udf: enabled: true echo: enabled: true host: ${services.default.host} port: 8089 baseUrl: ${services.default.protocol}://${services.echo.host}:${services.echo.port} cassandra: enabled: false inMemory: enabled: true cron: enabled: true timezone: ${global.spinnaker.timezone} notifications: mail: enabled: false host: fromAddress: hipchat: enabled: false url: token: botName: sms: enabled: false account: token: from: slack: enabled: false token: botName: deck: host: ${services.default.host} port: 9000 baseUrl: ${services.default.protocol}://${services.deck.host}:${services.deck.port} gateUrl: ${API_HOST:services.gate.baseUrl} bakeryUrl: ${services.bakery.baseUrl} timezone: ${global.spinnaker.timezone} auth: enabled: ${AUTH_ENABLED:false} fiat: enabled: false host: ${services.default.host} port: 7003 baseUrl: ${services.default.protocol}://${services.fiat.host}:${services.fiat.port} front50: host: ${services.default.host} port: 8080 baseUrl: ${services.default.protocol}://${services.front50.host}:${services.front50.port} storage_bucket: ${SPINNAKER_DEFAULT_STORAGE_BUCKET:} bucket_location: bucket_root: front50 cassandra: enabled: false redis: enabled: false gcs: enabled: false s3: enabled: false gate: host: ${services.default.host} port: 8084 baseUrl: ${services.default.protocol}://${services.gate.host}:${services.gate.port} igor: enabled: false host: ${services.default.host} port: 8088 baseUrl: ${services.default.protocol}://${services.igor.host}:${services.igor.port} kato: host: ${services.clouddriver.host} port: ${services.clouddriver.port} baseUrl: ${services.clouddriver.baseUrl} mort: host: ${services.clouddriver.host} port: ${services.clouddriver.port} baseUrl: ${services.clouddriver.baseUrl} orca: host: ${services.default.host} port: 8083 baseUrl: ${services.default.protocol}://${services.orca.host}:${services.orca.port} timezone: ${global.spinnaker.timezone} enabled: true oort: host: ${services.clouddriver.host} port: ${services.clouddriver.port} baseUrl: ${services.clouddriver.baseUrl} rosco: host: ${services.default.host} port: 8087 baseUrl: ${services.default.protocol}://${services.rosco.host}:${services.rosco.port} configDir: /opt/rosco/config/packer bakery: host: ${services.rosco.host} port: ${services.rosco.port} baseUrl: ${services.rosco.baseUrl} extractBuildDetails: true allowMissingPackageInstallation: false docker: targetRepository: jenkins: enabled: ${services.igor.enabled:false} defaultMaster: name: Jenkins baseUrl: username: password: redis: host: redis port: 6379 connection: ${REDIS_HOST:redis://localhost:6379} cassandra: host: ${services.default.host} port: 9042 embedded: false cluster: CASS_SPINNAKER travis: enabled: false defaultMaster: name: ci baseUrl: https://travis-ci.com address: https://api.travis-ci.org githubToken: spectator: webEndpoint: enabled: false stackdriver: enabled: ${SPINNAKER_STACKDRIVER_ENABLED:false} projectName: ${SPINNAKER_STACKDRIVER_PROJECT_NAME:${providers.google.primaryCredentials.project}} credentialsPath: ${SPINNAKER_STACKDRIVER_CREDENTIALS_PATH:${providers.google.primaryCredentials.jsonPath}} providers: aws: enabled: ${SPINNAKER_AWS_ENABLED:false} simpleDBEnabled: false defaultRegion: ${SPINNAKER_AWS_DEFAULT_REGION:us-west-2} defaultIAMRole: BaseIAMRole defaultSimpleDBDomain: CLOUD_APPLICATIONS primaryCredentials: name: default defaultKeyPairTemplate: "{{name}} -keypair" google: enabled: ${SPINNAKER_GOOGLE_ENABLED:false} defaultRegion: ${SPINNAKER_GOOGLE_DEFAULT_REGION:us-central1} defaultZone: ${SPINNAKER_GOOGLE_DEFAULT_ZONE:us-central1-f} primaryCredentials: name: my-account-name project: ${SPINNAKER_GOOGLE_PROJECT_ID:} jsonPath: ${SPINNAKER_GOOGLE_PROJECT_CREDENTIALS_PATH:} consul: enabled: ${SPINNAKER_GOOGLE_CONSUL_ENABLED:false} cf: enabled: false defaultOrg: spinnaker-cf-org defaultSpace: spinnaker-cf-space primaryCredentials: name: my-cf-account api: my-cf-api-uri console: my-cf-console-base-url azure: enabled: ${SPINNAKER_AZURE_ENABLED:false} defaultRegion: ${SPINNAKER_AZURE_DEFAULT_REGION:westus} primaryCredentials: name: my-azure-account clientId: appKey: tenantId: subscriptionId: titan: enabled: false defaultRegion: us-east-1 primaryCredentials: name: my-titan-account kubernetes: enabled: ${SPINNAKER_KUBERNETES_ENABLED:false} primaryCredentials: name: my-kubernetes-account namespace: default dockerRegistryAccount: ${providers.dockerRegistry.primaryCredentials.name} dockerRegistry: enabled: ${SPINNAKER_KUBERNETES_ENABLED:false} primaryCredentials: name: my-docker-registry-account address: ${SPINNAKER_DOCKER_REGISTRY:https://index.docker.io/ } repository: ${SPINNAKER_DOCKER_REPOSITORY:} username: ${SPINNAKER_DOCKER_USERNAME:} passwordFile: ${SPINNAKER_DOCKER_PASSWORD_FILE:} openstack: enabled: false defaultRegion: ${SPINNAKER_OPENSTACK_DEFAULT_REGION:RegionOne} primaryCredentials: name: my-openstack-account authUrl: ${OS_AUTH_URL} username: ${OS_USERNAME} password: ${OS_PASSWORD} projectName: ${OS_PROJECT_NAME} domainName: ${OS_USER_DOMAIN_NAME:Default} regions: ${OS_REGION_NAME:RegionOne} insecure: false
vim /var/k8s-yaml/armory/clouddriver/init-env.yaml
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 kind: ConfigMap apiVersion: v1 metadata: name: init-env namespace: armory data: API_HOST: http://spinnaker.od.com/api ARMORY_ID: c02f0781-92f5-4e80-86db-0ba8fe7b8544 ARMORYSPINNAKER_CONF_STORE_BUCKET: armory-platform ARMORYSPINNAKER_CONF_STORE_PREFIX: front50 ARMORYSPINNAKER_GCS_ENABLED: "false" ARMORYSPINNAKER_S3_ENABLED: "true" AUTH_ENABLED: "false" AWS_REGION: us-east-1 BASE_IP: 127.0.0.1 CLOUDDRIVER_OPTS: -Dspring.profiles.active=armory,configurator,local CONFIGURATOR_ENABLED: "false" DECK_HOST: http://spinnaker.od.com ECHO_OPTS: -Dspring.profiles.active=armory,configurator,local GATE_OPTS: -Dspring.profiles.active=armory,configurator,local IGOR_OPTS: -Dspring.profiles.active=armory,configurator,local PLATFORM_ARCHITECTURE: k8s REDIS_HOST: redis://redis:6379 SERVER_ADDRESS: 0.0.0.0 SPINNAKER_AWS_DEFAULT_REGION: us-east-1 SPINNAKER_AWS_ENABLED: "false" SPINNAKER_CONFIG_DIR: /home/spinnaker/config SPINNAKER_GOOGLE_PROJECT_CREDENTIALS_PATH: "" SPINNAKER_HOME: /home/spinnaker SPRING_PROFILES_ACTIVE: armory,configurator,local
vim /var/k8s-yaml/armory/clouddriver/custom-config.yaml
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 kind: ConfigMap apiVersion: v1 metadata: name: custom-config namespace: armory data: clouddriver-local.yml: | kubernetes: enabled: true accounts: - name: cluster-admin serviceAccount: false dockerRegistries: - accountName: harbor namespace: [] namespaces: - test - prod kubeconfigFile: /opt/spinnaker/credentials/custom/default-kubeconfig primaryAccount: cluster-admin dockerRegistry: enabled: true accounts: - name: harbor requiredGroupMembership: [] providerVersion: V1 insecureRegistry: true address: http://harbor.od.com username: admin password: Harbor12345 primaryAccount: harbor artifacts: s3: enabled: true accounts: - name: armory-config-s3-account apiEndpoint: http://minio-api.od.com apiRegion: us-east-1 gcs: enabled: false accounts: - name: armory-config-gcs-account custom-config.json: "" echo-configurator.yml: | diagnostics: enabled: true front50-local.yml: | spinnaker: s3: endpoint: http://minio-api.od.com igor-local.yml: | jenkins: enabled: true masters: - name: jenkins-admin address: http://jenkins.od.com username: admin password: admin123 primaryAccount: jenkins-admin nginx.conf: | gzip on; gzip_types text/plain text/css application/json application/x-javascript text/xml application/xml application/xml+rss text/javascript application/vnd.ms-fontobject application/x-font-ttf font/opentype image/svg+xml image/x-icon; server { listen 80; location / { proxy_pass http://armory-deck/; } location /api/ { proxy_pass http://armory-gate:8084/; } rewrite ^/login(.*)$ /api/login$1 last; rewrite ^/auth(.*)$ /api/auth$1 last; } spinnaker-local.yml: | services: igor: enabled: true
vim /var/k8s-yaml/armory/clouddriver/dp.yaml
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 107 apiVersion: apps/v1 kind: Deployment metadata: labels: app: armory-clouddriver name: armory-clouddriver namespace: armory spec: replicas: 1 revisionHistoryLimit: 7 selector: matchLabels: app: armory-clouddriver template: metadata: annotations: artifact.spinnaker.io/location: '"armory"' artifact.spinnaker.io/name: '"armory-clouddriver"' artifact.spinnaker.io/type: '"kubernetes/deployment"' moniker.spinnaker.io/application: '"armory"' moniker.spinnaker.io/cluster: '"clouddriver"' labels: app: armory-clouddriver spec: containers: - name: armory-clouddriver image: harbor.od.com/armory/clouddriver:v1.11.x imagePullPolicy: IfNotPresent command: - bash - -c args: - bash /opt/spinnaker/config/default/fetch.sh && cd /home/spinnaker/config && /opt/clouddriver/bin/clouddriver ports: - containerPort: 7002 protocol: TCP env: - name: JAVA_OPTS value: -Xmx2048M envFrom: - configMapRef: name: init-env livenessProbe: failureThreshold: 5 httpGet: path: /health port: 7002 scheme: HTTP initialDelaySeconds: 600 periodSeconds: 3 successThreshold: 1 timeoutSeconds: 1 readinessProbe: failureThreshold: 5 httpGet: path: /health port: 7002 scheme: HTTP initialDelaySeconds: 180 periodSeconds: 3 successThreshold: 5 timeoutSeconds: 1 securityContext: runAsUser: 0 volumeMounts: - mountPath: /etc/podinfo name: podinfo - mountPath: /home/spinnaker/.aws name: credentials - mountPath: /opt/spinnaker/credentials/custom name: default-kubeconfig - mountPath: /opt/spinnaker/config/default name: default-config - mountPath: /opt/spinnaker/config/custom name: custom-config imagePullSecrets: - name: harbor volumes: - configMap: defaultMode: 420 name: default-kubeconfig name: default-kubeconfig - configMap: defaultMode: 420 name: custom-config name: custom-config - configMap: defaultMode: 420 name: default-config name: default-config - name: credentials secret: defaultMode: 420 secretName: credentials - downwardAPI: defaultMode: 420 items: - fieldRef: apiVersion: v1 fieldPath: metadata.labels path: labels - fieldRef: apiVersion: v1 fieldPath: metadata.annotations path: annotations name: podinfo
vim /var/k8s-yaml/armory/clouddriver/svc.yaml
1 2 3 4 5 6 7 8 9 10 11 12 apiVersion: v1 kind: Service metadata: name: armory-clouddriver namespace: armory spec: ports: - port: 7002 protocol: TCP targetPort: 7002 selector: app: armory-clouddriver
应用资源配置清单 在任意一台k8s运算节点执行:
1 2 3 4 5 kubectl apply -f http://k8s-yaml.od.com/armory/clouddriver/init-env.yaml kubectl apply -f http://k8s-yaml.od.com/armory/clouddriver/default-config.yaml kubectl apply -f http://k8s-yaml.od.com/armory/clouddriver/custom-config.yaml kubectl apply -f http://k8s-yaml.od.com/armory/clouddriver/dp.yaml kubectl apply -f http://k8s-yaml.od.com/armory/clouddriver/svc.yaml
检查验证 1 2 3 4 5 docker ps -a|grep minio docker exec -it 6898f78d87 sh /]# curl armory-clouddriver:7002/health {"status":"UP","kubernetes":{"status":"UP"},"dockerRegistry":{"status":"UP"},"redisHealth":{"status":"UP","maxIdle":100,"minIdle":25,"numActive":0,"numIdle":3,"numWaiters":0},"diskSpace":{"status":"UP","total":20716716032,"free":12040998912,"threshold":10485760}}
部署spinnaker第三部分 spinnaker之front50部署 在k8s-dns.boysec.cn上:
1 2 3 docker pull armory/spinnaker-front50-slim:release-1.10.x-98b4ab9 docker tag armory/spinnaker-front50-slim:release-1.10.x-98b4ab9 harbor.od.com/armory/spinnaker-front50:v1.10.x docker push harbor.od.com/armory/spinnaker-front50:v1.10.x
准备资源配置清单 1 2 mkdir /var/k8s-yaml/armory/front50 cd /var/k8s-yaml/armory/front50
vim /var/k8s-yaml/armory/front50/dp.yaml
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 apiVersion: apps/v1 kind: Deployment metadata: labels: app: armory-front50 name: armory-front50 namespace: armory spec: replicas: 1 revisionHistoryLimit: 7 selector: matchLabels: app: armory-front50 template: metadata: annotations: artifact.spinnaker.io/location: '"armory"' artifact.spinnaker.io/name: '"armory-front50"' artifact.spinnaker.io/type: '"kubernetes/deployment"' moniker.spinnaker.io/application: '"armory"' moniker.spinnaker.io/cluster: '"front50"' labels: app: armory-front50 spec: containers: - name: armory-front50 image: harbor.od.com/armory/spinnaker-front50:v1.10.x imagePullPolicy: IfNotPresent command: - bash - -c args: - bash /opt/spinnaker/config/default/fetch.sh && cd /home/spinnaker/config && /opt/front50/bin/front50 ports: - containerPort: 8080 protocol: TCP env: - name: JAVA_OPTS value: -javaagent:/opt/front50/lib/jamm-0.2.5.jar -Xmx1000m envFrom: - configMapRef: name: init-env livenessProbe: failureThreshold: 3 httpGet: path: /health port: 8080 scheme: HTTP initialDelaySeconds: 600 periodSeconds: 3 successThreshold: 1 timeoutSeconds: 1 readinessProbe: failureThreshold: 3 httpGet: path: /health port: 8080 scheme: HTTP initialDelaySeconds: 180 periodSeconds: 5 successThreshold: 8 timeoutSeconds: 1 volumeMounts: - mountPath: /etc/podinfo name: podinfo - mountPath: /home/spinnaker/.aws name: credentials - mountPath: /opt/spinnaker/config/default name: default-config - mountPath: /opt/spinnaker/config/custom name: custom-config imagePullSecrets: - name: harbor volumes: - configMap: defaultMode: 420 name: custom-config name: custom-config - configMap: defaultMode: 420 name: default-config name: default-config - name: credentials secret: defaultMode: 420 secretName: credentials - downwardAPI: defaultMode: 420 items: - fieldRef: apiVersion: v1 fieldPath: metadata.labels path: labels - fieldRef: apiVersion: v1 fieldPath: metadata.annotations path: annotations name: podinfo
vim /var/k8s-yaml/armory/front50/svc.yaml
1 2 3 4 5 6 7 8 9 10 11 12 apiVersion: v1 kind: Service metadata: name: armory-front50 namespace: armory spec: ports: - port: 8080 protocol: TCP targetPort: 8080 selector: app: armory-front50
应用资源配置清单 在任意一台k8s运算节点执行:
1 2 kubectl apply -f http://k8s-yaml.od.com/armory/front50/dp.yaml kubectl apply -f http://k8s-yaml.od.com/armory/front50/svc.yaml
检查验证 1 2 3 4 5 ~]# docker ps -qa|grep minio 6898f78d87 ~]# docker exec -it 6898f78d87 sh / # curl armory-front50:8080/health {"status":"UP"}
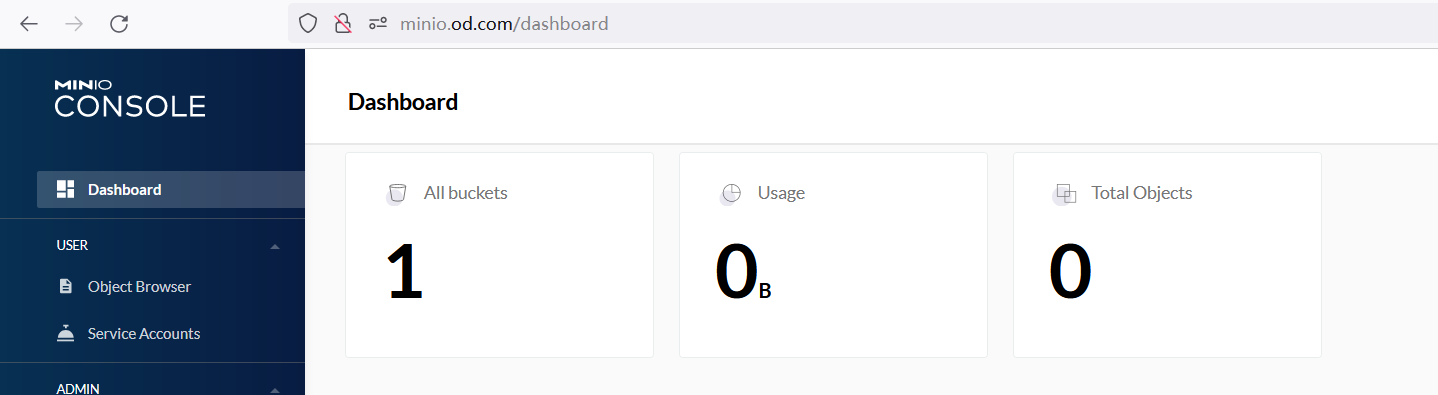
访问http://minio.od.com 会发现有一个空间
spinnaker之orca部署 准备docker镜像 1 2 3 docker pull armory/spinnaker-orca-slim:release-1.10.x-769f4e5 docker tag armory/spinnaker-orca-slim:release-1.10.x-769f4e5 harbor.od.com/armory/spinnaker-orca:v1.10.x docker push harbor.od.com/armory/spinnaker-orca:v1.10.x
准备资源配置清单 1 2 mkdir /var/k8s-yaml/armory/orca cd /var/k8s-yaml/armory/orca
vim /var/k8s-yaml/armory/orca/dp.yaml
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 apiVersion: apps/v1 kind: Deployment metadata: labels: app: armory-orca name: armory-orca namespace: armory spec: replicas: 1 revisionHistoryLimit: 7 selector: matchLabels: app: armory-orca template: metadata: annotations: artifact.spinnaker.io/location: '"armory"' artifact.spinnaker.io/name: '"armory-orca"' artifact.spinnaker.io/type: '"kubernetes/deployment"' moniker.spinnaker.io/application: '"armory"' moniker.spinnaker.io/cluster: '"orca"' labels: app: armory-orca spec: containers: - name: armory-orca image: harbor.od.com/armory/spinnaker-orca:v1.10.x imagePullPolicy: IfNotPresent command: - bash - -c args: - bash /opt/spinnaker/config/default/fetch.sh && cd /home/spinnaker/config && /opt/orca/bin/orca ports: - containerPort: 8083 protocol: TCP env: - name: JAVA_OPTS value: -Xmx1000M envFrom: - configMapRef: name: init-env livenessProbe: failureThreshold: 5 httpGet: path: /health port: 8083 scheme: HTTP initialDelaySeconds: 600 periodSeconds: 5 successThreshold: 1 timeoutSeconds: 1 readinessProbe: failureThreshold: 3 httpGet: path: /health port: 8083 scheme: HTTP initialDelaySeconds: 180 periodSeconds: 3 successThreshold: 5 timeoutSeconds: 1 volumeMounts: - mountPath: /etc/podinfo name: podinfo - mountPath: /opt/spinnaker/config/default name: default-config - mountPath: /opt/spinnaker/config/custom name: custom-config imagePullSecrets: - name: harbor volumes: - configMap: defaultMode: 420 name: custom-config name: custom-config - configMap: defaultMode: 420 name: default-config name: default-config - downwardAPI: defaultMode: 420 items: - fieldRef: apiVersion: v1 fieldPath: metadata.labels path: labels - fieldRef: apiVersion: v1 fieldPath: metadata.annotations path: annotations name: podinfo
vim /var/k8s-yaml/armory/orca/svc.yaml
1 2 3 4 5 6 7 8 9 10 11 12 apiVersion: v1 kind: Service metadata: name: armory-orca namespace: armory spec: ports: - port: 8083 protocol: TCP targetPort: 8083 selector: app: armory-orca
应用资源配置清单 在任意一台k8s运算节点执行:
1 2 kubectl apply -f http://k8s-yaml.od.com/armory/orca/dp.yaml kubectl apply -f http://k8s-yaml.od.com/armory/orca/svc.yaml
检查验证 1 2 3 ~]# docker exec -it 6898f78d87 sh / # curl armory-orca:8083/health {"status":"UP"}
spinnaker之echo部署 准备docker镜像 1 2 3 docker pull armory/echo-armory:5891816-release-1.10.x-a568cf9 docker tag armory/echo-armory:5891816-release-1.10.x-a568cf9 harbor.od.com/armory/echo:v1.10.x docker push harbor.od.com/armory/echo:v1.10.x
准备资源配置清单 1 2 mkdir /var/k8s-yaml/armory/echo cd /var/k8s-yaml/armory/echo
vim /var/k8s-yaml/armory/echo/dp.yaml
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 apiVersion: apps/v1 kind: Deployment metadata: labels: app: armory-echo name: armory-echo namespace: armory spec: replicas: 1 revisionHistoryLimit: 7 selector: matchLabels: app: armory-echo template: metadata: annotations: artifact.spinnaker.io/location: '"armory"' artifact.spinnaker.io/name: '"armory-echo"' artifact.spinnaker.io/type: '"kubernetes/deployment"' moniker.spinnaker.io/application: '"armory"' moniker.spinnaker.io/cluster: '"echo"' labels: app: armory-echo spec: containers: - name: armory-echo image: harbor.od.com/armory/echo:v1.10.x imagePullPolicy: IfNotPresent command: - bash - -c args: - bash /opt/spinnaker/config/default/fetch.sh && cd /home/spinnaker/config && /opt/echo/bin/echo ports: - containerPort: 8089 protocol: TCP envFrom: - configMapRef: name: init-env livenessProbe: failureThreshold: 3 httpGet: path: /health port: 8089 scheme: HTTP initialDelaySeconds: 600 periodSeconds: 3 successThreshold: 1 timeoutSeconds: 1 readinessProbe: failureThreshold: 3 httpGet: path: /health port: 8089 scheme: HTTP initialDelaySeconds: 180 periodSeconds: 3 successThreshold: 5 timeoutSeconds: 1 volumeMounts: - mountPath: /etc/podinfo name: podinfo - mountPath: /opt/spinnaker/config/default name: default-config - mountPath: /opt/spinnaker/config/custom name: custom-config imagePullSecrets: - name: harbor volumes: - configMap: defaultMode: 420 name: custom-config name: custom-config - configMap: defaultMode: 420 name: default-config name: default-config - downwardAPI: defaultMode: 420 items: - fieldRef: apiVersion: v1 fieldPath: metadata.labels path: labels - fieldRef: apiVersion: v1 fieldPath: metadata.annotations path: annotations name: podinfo
vim /var/k8s-yaml/armory/echo/svc.yaml
1 2 3 4 5 6 7 8 9 10 11 12 apiVersion: v1 kind: Service metadata: name: armory-echo namespace: armory spec: ports: - port: 8089 protocol: TCP targetPort: 8089 selector: app: armory-echo
应用资源配置清单 在任意一台k8s运算节点执行:
1 2 kubectl apply -f http://k8s-yaml.od.com/armory/echo/dp.yaml kubectl apply -f http://k8s-yaml.od.com/armory/echo/svc.yaml
检查验证 1 2 3 docker exec -it 6898f78d87 sh / # curl armory-echo:8089/health {"status":"UP"}
spinnaker之igor部署 准备docker镜像 1 2 3 docker pull armory/spinnaker-igor-slim:release-1.10.x-a4fd897 docker tag armory/spinnaker-igor-slim:release-1.10.x-a4fd897 harbor.od.com/armory/spinnaker-igor:v1.10.x docker push harbor.od.com/armory/spinnaker-igor:v1.10.x
准备资源配置清单 1 2 mkdir /var/k8s-yaml/armory/igor cd /var/k8s-yaml/armory/igor
vim /var/k8s-yaml/armory/igor/dp.yaml
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 apiVersion: apps/v1 kind: Deployment metadata: labels: app: armory-igor name: armory-igor namespace: armory spec: replicas: 1 revisionHistoryLimit: 7 selector: matchLabels: app: armory-igor template: metadata: annotations: artifact.spinnaker.io/location: '"armory"' artifact.spinnaker.io/name: '"armory-igor"' artifact.spinnaker.io/type: '"kubernetes/deployment"' moniker.spinnaker.io/application: '"armory"' moniker.spinnaker.io/cluster: '"igor"' labels: app: armory-igor spec: containers: - name: armory-igor image: harbor.od.com/armory/spinnaker-igor:v1.10.x imagePullPolicy: IfNotPresent command: - bash - -c args: - bash /opt/spinnaker/config/default/fetch.sh && cd /home/spinnaker/config && /opt/igor/bin/igor ports: - containerPort: 8088 protocol: TCP env: - name: IGOR_PORT_MAPPING value: -8088 :8088 - name: JAVA_OPTS value: -Xmx1000M envFrom: - configMapRef: name: init-env livenessProbe: failureThreshold: 3 httpGet: path: /health port: 8088 scheme: HTTP initialDelaySeconds: 600 periodSeconds: 3 successThreshold: 1 timeoutSeconds: 1 readinessProbe: failureThreshold: 3 httpGet: path: /health port: 8088 scheme: HTTP initialDelaySeconds: 180 periodSeconds: 5 successThreshold: 5 timeoutSeconds: 1 volumeMounts: - mountPath: /etc/podinfo name: podinfo - mountPath: /opt/spinnaker/config/default name: default-config - mountPath: /opt/spinnaker/config/custom name: custom-config imagePullSecrets: - name: harbor securityContext: runAsUser: 0 volumes: - configMap: defaultMode: 420 name: custom-config name: custom-config - configMap: defaultMode: 420 name: default-config name: default-config - downwardAPI: defaultMode: 420 items: - fieldRef: apiVersion: v1 fieldPath: metadata.labels path: labels - fieldRef: apiVersion: v1 fieldPath: metadata.annotations path: annotations name: podinfo
vim /var/k8s-yaml/armory/igor/svc.yaml
1 2 3 4 5 6 7 8 9 10 11 12 apiVersion: v1 kind: Service metadata: name: armory-igor namespace: armory spec: ports: - port: 8088 protocol: TCP targetPort: 8088 selector: app: armory-igor
应用资源配置清单 在任意一台k8s运算节点执行:
1 2 kubectl apply -f http://k8s-yaml.od.com/armory/igor/dp.yaml kubectl apply -f http://k8s-yaml.od.com/armory/igor/svc.yaml
检查验证 1 2 3 ~]# docker exec -it 6898f78d87 sh / # curl armory-igor:8088/health {"status":"UP"}
spinnaker之gate部署 准备docker镜像 1 2 3 docker pull armory/gate-armory:1.10.2-5b9fb1b-9dfb915-rc392 docker tag armory/gate-armory:1.10.2-5b9fb1b-9dfb915-rc392 harbor.od.com/armory/gate:v1.10.x
准备资源配置清单 1 2 mkdir /var/k8s-yaml/armory/gate cd /var/k8s-yaml/armory/gate
vim /var/k8s-yaml/armory/gate/dp.yaml
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 102 103 104 105 106 apiVersion: apps/v1 kind: Deployment metadata: labels: app: armory-gate name: armory-gate namespace: armory spec: replicas: 1 revisionHistoryLimit: 7 selector: matchLabels: app: armory-gate template: metadata: annotations: artifact.spinnaker.io/location: '"armory"' artifact.spinnaker.io/name: '"armory-gate"' artifact.spinnaker.io/type: '"kubernetes/deployment"' moniker.spinnaker.io/application: '"armory"' moniker.spinnaker.io/cluster: '"gate"' labels: app: armory-gate spec: containers: - name: armory-gate image: harbor.od.com/armory/gate:v1.10.x imagePullPolicy: IfNotPresent command: - bash - -c args: - bash /opt/spinnaker/config/default/fetch.sh gate && cd /home/spinnaker/config && /opt/gate/bin/gate ports: - containerPort: 8084 name: gate-port protocol: TCP - containerPort: 8085 name: gate-api-port protocol: TCP env: - name: GATE_PORT_MAPPING value: -8084 :8084 - name: GATE_API_PORT_MAPPING value: -8085 :8085 - name: JAVA_OPTS value: -Xmx1000M envFrom: - configMapRef: name: init-env livenessProbe: exec: command: - /bin/bash - -c - wget -O - http://localhost:8084/health || wget -O - https://localhost:8084/health failureThreshold: 5 initialDelaySeconds: 600 periodSeconds: 5 successThreshold: 1 timeoutSeconds: 1 readinessProbe: exec: command: - /bin/bash - -c - wget -O - http://localhost:8084/health?checkDownstreamServices=true&downstreamServices=true || wget -O - https://localhost:8084/health?checkDownstreamServices=true&downstreamServices=true failureThreshold: 3 initialDelaySeconds: 180 periodSeconds: 5 successThreshold: 10 timeoutSeconds: 1 volumeMounts: - mountPath: /etc/podinfo name: podinfo - mountPath: /opt/spinnaker/config/default name: default-config - mountPath: /opt/spinnaker/config/custom name: custom-config imagePullSecrets: - name: harbor securityContext: runAsUser: 0 volumes: - configMap: defaultMode: 420 name: custom-config name: custom-config - configMap: defaultMode: 420 name: default-config name: default-config - downwardAPI: defaultMode: 420 items: - fieldRef: apiVersion: v1 fieldPath: metadata.labels path: labels - fieldRef: apiVersion: v1 fieldPath: metadata.annotations path: annotations name: podinfo
vim /var/k8s-yaml/armory/gate/svc.yaml
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 apiVersion: v1 kind: Service metadata: name: armory-gate namespace: armory spec: ports: - name: gate-port port: 8084 protocol: TCP targetPort: 8084 - name: gate-api-port port: 8085 protocol: TCP targetPort: 8085 selector: app: armory-gate
应用资源配置清单 在任意一台k8s运算节点执行:
1 2 kubectl apply -f http://k8s-yaml.od.com/armory/gate/dp.yaml kubectl apply -f http://k8s-yaml.od.com/armory/gate/svc.yaml
检查验证 1 2 3 ~]# docker exec -it 6898f78d87 sh / # curl armory-gate:8084/health {"status":"UP"}
spinnaker之deck部署 准备docker镜像 1 2 3 docker pull armory/deck-armory:12927b8-release-1.10.x-c9abb38e5 docker tag armory/deck-armory:12927b8-release-1.10.x-c9abb38e5 harbor.od.com/armory/deck:v1.10.x docker push harbor.od.com/armory/deck:v1.10.x
准备资源配置清单 经过测试1.10不行,未深入研究。1.8可以
1 2 mkdir /var/k8s-yaml/armory/deck cd /var/k8s-yaml/armory/deck
vim /var/k8s-yaml/armory/deck/dp.yaml
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 86 87 88 89 apiVersion: apps/v1 kind: Deployment metadata: labels: app: armory-deck name: armory-deck namespace: armory spec: replicas: 1 revisionHistoryLimit: 7 selector: matchLabels: app: armory-deck template: metadata: annotations: artifact.spinnaker.io/location: '"armory"' artifact.spinnaker.io/name: '"armory-deck"' artifact.spinnaker.io/type: '"kubernetes/deployment"' moniker.spinnaker.io/application: '"armory"' moniker.spinnaker.io/cluster: '"deck"' labels: app: armory-deck spec: containers: - name: armory-deck image: harbor.od.com/armory/deck:v1.10.x imagePullPolicy: IfNotPresent command: - bash - -c args: - bash /opt/spinnaker/config/default/fetch.sh && /bin/sh -c bin/run-apache2.sh ports: - containerPort: 9000 protocol: TCP envFrom: - configMapRef: name: init-env livenessProbe: failureThreshold: 3 httpGet: path: / port: 9000 scheme: HTTP initialDelaySeconds: 180 periodSeconds: 3 successThreshold: 1 timeoutSeconds: 1 readinessProbe: failureThreshold: 5 httpGet: path: / port: 9000 scheme: HTTP initialDelaySeconds: 30 periodSeconds: 3 successThreshold: 5 timeoutSeconds: 1 volumeMounts: - mountPath: /etc/podinfo name: podinfo - mountPath: /opt/spinnaker/config/default name: default-config - mountPath: /opt/spinnaker/config/custom name: custom-config imagePullSecrets: - name: harbor volumes: - configMap: defaultMode: 420 name: custom-config name: custom-config - configMap: defaultMode: 420 name: default-config name: default-config - downwardAPI: defaultMode: 420 items: - fieldRef: apiVersion: v1 fieldPath: metadata.labels path: labels - fieldRef: apiVersion: v1 fieldPath: metadata.annotations path: annotations name: podinfo
vim /var/k8s-yaml/armory/deck/svc.yaml
1 2 3 4 5 6 7 8 9 10 11 12 apiVersion: v1 kind: Service metadata: name: armory-deck namespace: armory spec: ports: - port: 80 protocol: TCP targetPort: 9000 selector: app: armory-deck
应用资源配置清单 在任意一台k8s运算节点执行:
1 2 kubectl apply -f http://k8s-yaml.od.com/armory/deck/dp.yaml kubectl apply -f http://k8s-yaml.od.com/armory/deck/svc.yaml
检查验证 1 2 3 ~]# docker exec -it 6898f78d87 sh / # curl armory-igor:8088/health {"status":"UP"}
spinnaker之nginx部署 准备docker镜像 1 2 3 docker pull nginx:1.15.12 docker tag nginx:1.15.12 harbor.od.com/armory/nginx:v1.15.12 docker push harbor.od.com/armory/nginx:v1.15.12
准备资源配置清单 1 2 mkdir /var/k8s-yaml/armory/nginx cd /var/k8s-yaml/armory/nginx
vim /var/k8s-yaml/armory/nginx/dp.yaml
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 apiVersion: apps/v1 kind: Deployment metadata: labels: app: armory-nginx name: armory-nginx namespace: armory spec: replicas: 1 revisionHistoryLimit: 7 selector: matchLabels: app: armory-nginx template: metadata: annotations: artifact.spinnaker.io/location: '"armory"' artifact.spinnaker.io/name: '"armory-nginx"' artifact.spinnaker.io/type: '"kubernetes/deployment"' moniker.spinnaker.io/application: '"armory"' moniker.spinnaker.io/cluster: '"nginx"' labels: app: armory-nginx spec: containers: - name: armory-nginx image: harbor.od.com/armory/nginx:v1.15.12 imagePullPolicy: Always command: - bash - -c args: - bash /opt/spinnaker/config/default/fetch.sh nginx && nginx -g 'daemon off;' ports: - containerPort: 80 name: http protocol: TCP - containerPort: 443 name: https protocol: TCP - containerPort: 8085 name: api protocol: TCP livenessProbe: failureThreshold: 3 httpGet: path: / port: 80 scheme: HTTP initialDelaySeconds: 180 periodSeconds: 3 successThreshold: 1 timeoutSeconds: 1 readinessProbe: failureThreshold: 3 httpGet: path: / port: 80 scheme: HTTP initialDelaySeconds: 30 periodSeconds: 3 successThreshold: 5 timeoutSeconds: 1 volumeMounts: - mountPath: /opt/spinnaker/config/default name: default-config - mountPath: /etc/nginx/conf.d name: custom-config imagePullSecrets: - name: harbor volumes: - configMap: defaultMode: 420 name: custom-config name: custom-config - configMap: defaultMode: 420 name: default-config name: default-config
vim /var/k8s-yaml/armory/nginx/svc.yaml
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 apiVersion: v1 kind: Service metadata: name: armory-nginx namespace: armory spec: ports: - name: http port: 80 protocol: TCP targetPort: 80 - name: https port: 443 protocol: TCP targetPort: 443 - name: api port: 8085 protocol: TCP targetPort: 8085 selector: app: armory-nginx
vim /var/k8s-yaml/armory/nginx/ingress.yaml
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 apiVersion: extensions/v1beta1 kind: Ingress metadata: labels: app: spinnaker web: spinnaker.od.com name: armory-nginx namespace: armory spec: rules: - host: spinnaker.od.com http: paths: - backend: serviceName: armory-nginx servicePort: 80
应用资源配置清单 1 2 3 kubectl apply -f http://k8s-yaml.od.com/armory/nginx/dp.yaml kubectl apply -f http://k8s-yaml.od.com/armory/nginx/svc.yaml kubectl apply -f http://k8s-yaml.od.com/armory/nginx/ingress.yaml
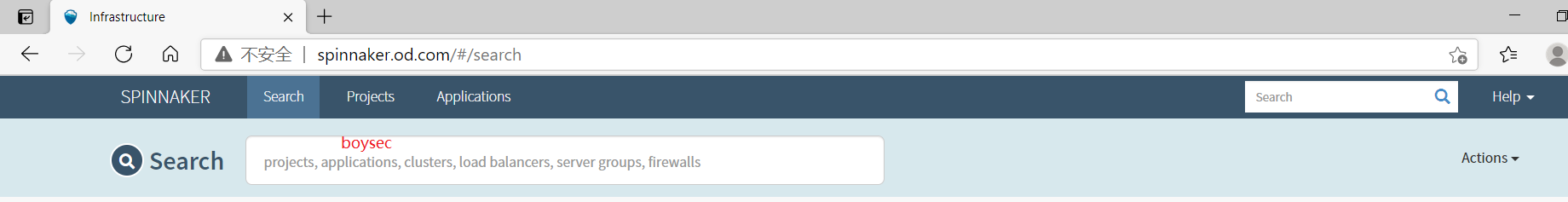
配置DNS解析 1 2 3 [root@k8s-dns ~]# vi /var/named/chroot/etc/od.com.zone ... spinnaker A 10.1.1.50
打开浏览器验证 http://spinnaker.od.com